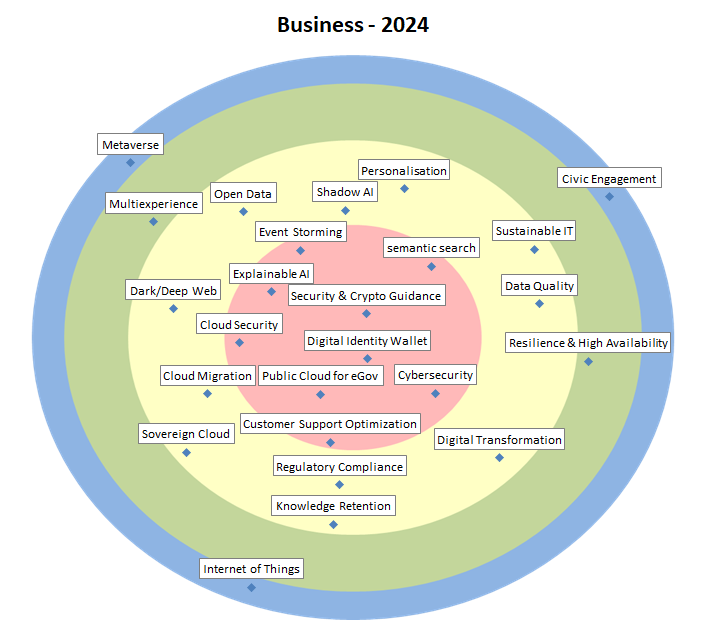
Business Goals, Problems, Opportunities…
| Security & Crypto Guidance | = | Correct implementation of secure systems as well as correct application of cryptographic algorithms is a complex and continuously evolving endeavour which requires expert knowledge. In order to streamline this, security & crypto guidelines are indispensable. |
| Digital Identity Wallet | = | Digital identity wallets (DIW) enable the sharing of identity data and all kinds of attestations across any number of organisations and use cases. Through the European DIW, citizens will be able to prove their identity and share information from their DIW, while staying in control of their data. |
| Cloud Security | = | A sub-domain of cloud computing, encompassing all aspects of security and cryptography related to cloud computing, whether private, public or hybrid. |
| Cybersecurity | = | Cybersecurity is composed of technologies, processes, and practices designed to protect networks, computers, applications, and data from attack, damage or unauthorised access. Defence against powerful and organised attackers is gaining importance. Ransomware is a worrying trend. |
| Customer Support Optimization | = | Customer support optimization is the process of enhancing the efficiency and effectiveness of customer service, aiming for improved customer satisfaction. It encompasses improving self-service as well as agent assist tools like semantic knowledge base search and response suggestions. |
| Explainable AI | = | Explainable AI refers to methods and techniques that make outputs of AI systems more understandable to humans, thereby increasing trust. Key aspects include transparency, interpretability, accountability, fairness and visualizations. |
| Public Cloud for eGov | = | We see also in Belgium a tendency (or desire) of government organisations in using public cloud infrastructure and applications. But GDPR legislation, and privacy-issues can be a killjoy… |
| Event Storming | + | Proliferation of APIs and integrations necessitates better coordination between products/teams. Event storming, in which a business process is “stormed out” as a series of domain events, can rapidly identify key concepts in a problem space and align a variety of stakeholders. |
| semantic search | N | A search technique that goes beyond keyword search. Semantic search allows for a better understanding of the user’s intent and the query context. |
| Personalisation | – | The goal of personalisation is to accomplish a relevant and individualised interaction between an organisation and her target audience in order to improve the user experience. |
| Sustainable IT | = | IT has a twofold impact on the current ecological crisis. It may reduce the ecological footprint of existing processes, but it has a considerable ecological footprint throughout its lifecycle (e.g., mining, energy usage, waste). Public sector should maximise the first and minimise the second. |
| Data Quality | = | Tools, methods and architectures to evaluate, improve and monitor data quality and to manage information, taking into account cost-benefit ratio and fitness for use (Includes Master Data Management). |
| Digital Transformation | = | By exploiting the latest technologies (like IoT, analytics, machine learning…), business models can be changed/transformed and new robust digital business models can be created. |
| Knowledge Retention | = | When an employee leaves an organisation, so does a part of an organisation’s intellectual capital. Knowledge retention is a specific process within wider knowledge management activities concerned with persevering that intellectual capital. |
| Regulatory Compliance | = | The number of regulations is increasing; GDPR, NIS2 and the Data Governance Act are a few notable examples. Compliance with all applicable regulations becomes increasingly challenging. |
| Sovereign Cloud | = | Sovereign cloud is the provisioning of cloud services in compliance with local laws and regulations regarding data security and privacy, so that data remains under sovereign control and jurisdiction, preventing access to data by foreign authorities. |
| Cloud Migration | + | As the pressure to move solutions to the Public Cloud increases, so does the inherent danger of vendor lock-in. Therefore, Cloud Migration strategies and techniques become a more important defensive measure to safeguard an enterprise’s flexibility in choosing Cloud Service Providers. |
| Dark/Deep Web | + | The deep web is the part of the Web not indexed by search engines. The dark web is the deep web only accessible with specific software, configurations, or authorisation. Both are mostly used for criminal activities, such as drug fraud, illicit work, hacking preparations & trade of stolen data. |
| Open Data | + | Data interoperability based on documented “open data” for citizens, enterprises, … (and in some cases based on web semantics norms). One of the most important forms of open data is open government data. Mostly there are severe data quality issues. |
| Shadow AI | + | The phenomenon where individuals (e.g. ‘citizen data scientists’) use easy-to-use tools to develop their own AI-solutions and models. Very powerful for the business, but also dangerous for an untrained audience and in the context of ethical decisions and biased data. |
| Resilience & High Availability | – | High availability is a characteristic of a system, which aims to ensure an agreed level of operational performance, usually uptime, for a higher-than-normal period. Modernisation has resulted in an increased reliance on these systems. |
| Multiexperience | = | Refers to a user’s whole experience with one application across a variety of digital touchpoints—websites, apps, chatbots, AR/VR, wearables—using a combination of interaction modalities, like touch, voice, vision, and motion. Purpose: support a seamless and consistent user journey. |
| Civic Engagement | – | The use of IT to stimulate voluntary participation and self-organisation of citizens to create societal added value. The citizen can assume one or more roles, such as data provider. |
| Internet of Things | = | With the Internet of Things (IoT), many electromechanical objects, along with a vast number of sensors and actuators, become connected to the internet and generate an abundance of data, potentially impacting existing businesses while allowing new ones. |
| Metaverse | = | A converged network of virtual-reality spaces or augmented reality where users can interact with a computer-generated environment and other users to socialise, buy (virtual) goods, perform work-related activities, etc. |