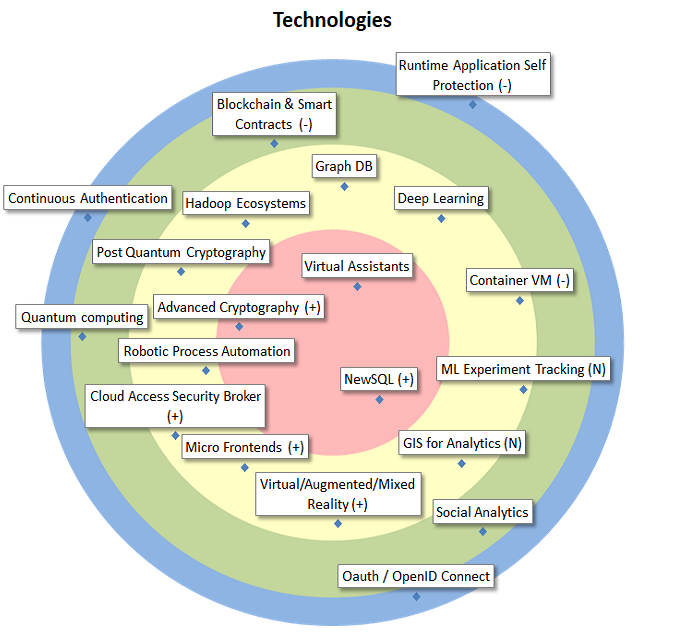
| Advanced Cryptography |
Advanced cryptography is cryptography that goes beyond the well known crypto work horses such as digital signatures. It allows to reconcile functional requirements with strong security and privacy requirements, which is would otherwise be impossible or at least very complex. |
| NewSQL |
NewSQL Databases combine the scalability and performance of NOSQL DB’s with the ACID principles of RDBMS. Like the traditional DB’s, they support the relational model and SQL. This makes them more suited to replace these DB’s in older applications being re-engineered to increase resilience. |
| Virtual Assistants |
Reply automatically to questions or utterances, using a conversational interface as basic channel, that accepts chat or speech. Possible applications are: website guidance, helpdesk assistance, querying analytics systems (conversational analytics), or simplification of procedures. |
| Cloud Access Security Broker |
On-premises or cloud-based security policy enforcement point, placed between cloud service consumers and cloud service providers to combine and interject enterprise security policies as the cloud-based resources are accessed. This point could do encryption and/or pseudonymization. |
| Container VM |
Containers are not perfectly isolated, virtual machines are too heavyweight. Container VM technology aims to bridge the gap by making very lightweight but well isolated vm’s, perfectly suited to run a container. Useful for multitenant Kubernetes and FPaaS platforms. |
| Deep Learning |
Important focus area of AI. Architectures such as Recurrent/Convolutional Neural Nets, GANs, etc. learn hierarchical representations of the data, corresponding to different levels of abstractions, largely from the raw data. Toolkits include TensorFlow, Caffe, Keras,… |
| GIS for Analytics |
Analytical software that integrates with GIS (Geographical Information Systems). Allows to represent the results of the analytical software geographically. |
| Graph DB |
Databases based on and/or oriented towards graphs, with nodes (entities) connected through edges (relations). They are very useful in graph analytics, but could also serve in miscellaneous production systems. |
| Hadoop Ecosystems |
Hadoop Ecosystems implement Big Data distributed storage (HDFS), access (Hive, Impala), distributed computing (MapReduce, Spark), transfer (Sqoop, Kafka, Flume), configuration, monitoring, and management modules, in one integrated environment consisting of several nodes. |
| Micro Frontends |
In analogy with microservices on the server side, micro front-ends allow the piecemeal development and deployment of an end-user application. The success of this technology will be determined by the quality of the frameworks/platforms combining these ‘pieces’. |
| ML Experiment Tracking |
Een goed model bekomen bij Machine Learning omvat nog steeds veel experimenteren. Momenteel ontstaan er handige tools om deze experimenten gestroomlijnder te kunnen beheren. |
| Post Quantum Cryptography |
Cryptographic algorithms considered secure against an attack performed by a quantum computer. |
| Robotic Process Automation |
Robotic Process Automation is a process automation technology in which software robots can take over keyboard/mouse and other controls to simulate the work of human workers, enabling automation without altering existing systems. |
| Virtual/Augmented/Mixed Reality |
UI technologies offering an immersive experience, using altered or completely simulated environments in which the user senses and interacts with virtual entities. Potential uses in public sector could be (explorational) Analytics and field work (inspection). |
| Blockchain & Smart Contracts |
Blockchain & smart contracts technology enable a reduction or even elimination of central or intermediary parties. Storage & computation are performed by multiple parties in a network. A verification mechanisms guarantees the correct application of the rules & tamper-proofness of the data. |
| Quantum computing |
Quantum computing is based on quantum-mechanical phenomena. It might in the future allow more powerful simulations and analysis than today. Its different fundamentals are reflected in new programming languages such as Q#. |
| Social Analytics |
The automatic processing and analysis of data from internal and external social media to extract useful information. Most of Big Data Analytics solutions have connectors to exploit these kinds of resources. |
| Continuous Authentication |
Methods for continuous verification whether the same specific person who logged into a device is still using it. |
| Oauth / OpenID Connect |
Standards for authentication / authorization relevant in the domains of mobile applications and REST architectures. |
| Runtime Application Self Protection |
Runtime Application Self Protection (RASP) is a security technology that is built or linked into an application or application runtime environment, and is capable of controlling application execution and detecting and preventing real-time attacks. |