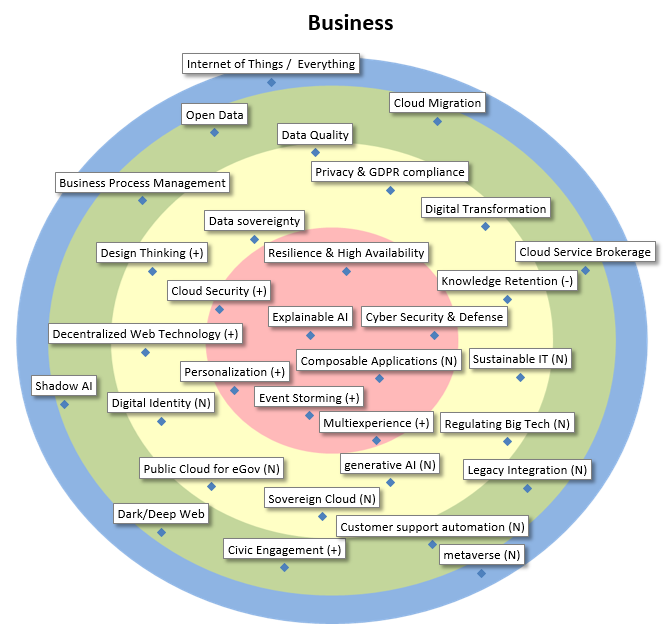
Business Goals, Problems, Opportunities…
| Cyber Security & Defense | Cyber security is composed of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access. Due to the rise of cyber warfare, defense against powerful attackers gains importance. |
| Resilience & High Availability | High availability is a characteristic of a system, which aims to ensure an agreed level of operational performance, usually uptime, for a higher than normal period. Modernization has resulted in an increased reliance on these systems. |
| Explainable AI | Public sector’s business needs require any deployed AI system to be robust and explainable. To this end we investigate existing and upcoming tools that increase transparency of AI systems towards the end user. |
| Cloud Security | Sub-domain of Cloud Computing, encompassing all aspects related to the security of and cryptography in the cloud, whether private, public or hybrid. |
| Personalization | The goal of personalization is to accomplish a relevant and individualized interaction between an organization and her target audience in order to improve the user experience. |
| Event Storming | Proliferation of APIs and integrations necessitates better coordination between products/teams. Event storming, in which a business process is “stormed out” as a series of domain events, can rapidly identify key concepts in a problem space and align a variety of stakeholders. |
| Multiexperience | Refers to a user’s whole experience with one application across a variety of digital touchpoints—websites, apps, chatbots, AR/VR, wearables—using a combination of interaction modalities, like touch, voice, vision, and motion. Purpose: support a seamless and consistent user journey. |
| Composable Applications | Applications composed of business-oriented building blocks, where these modular reusable blocks are independent one of another and can be configured by Business and IT into a solution. Main advantage is the support for agility of the business to changes while resilience should be maintained. |
| Knowledge Retention | When an employee leaves an organization, so does a part of an organization’s intellectual capital. Knowledge retention is a specific process within wider knowledge management activities concerned with persevering that intellectual capital. |
| Digital Transformation | By exploiting the latestl technologies (like IoT, analytics, machine learning…), business models can be changed/transformed and new robust digital business models can be created. |
| Privacy & GDPR compliance | Due to technological evolutions, protection of personal data is moving target that should continuously have our attention. Since may 2018, the GDPR is in force, which provides the legal framework, including obligations and potentially fines for enterprises. |
| Data Quality | Tools, methods and architectures to evaluate, improve and monitor data quality and to manage information, taking into account cost-benefit ratio and fitness for use (Includes Master Data Management). |
| Data sovereignty | Data sovereignty is the idea that data are subject to the laws and governance structures within the nation it is collected. The concept of data sovereignty is closely linked with data security, cloud computing and technological sovereignty. |
| Design Thinking | Used to improve the design from software to products and services. Empathy for users and the gathering of insight into their needs and motivations is crucial. Used for digital innovation with focus on people. Closely related to Human-Centered Design and the uptake of (government) applications. |
| Decentralized Web Technology | Set of web-based technologies to let people control their data and choose the applications and services to use with it, enabling a level-playing field for innovation and enabling people to regain control of their own data. Supporting technologies are SOLID and SSI (Self-Sovereign Identity). |
| Digital Identity | Citizens have lots of fragmented personal data, constituting their digital identity. Can they obtain transparency, and if required, control? Novel supporting technologies are i.a. SOLID and blockchain-based identity systems. Traditional and centralized approach remain useful. |
| Public Cloud for eGov | We see also in Belgium a tendency (or desire) of government organisations in using public cloud infrastructure and applications. But GDPR legislation, and privacy-issues can be a killjoy… |
| Sovereign Cloud | Public Cloud Environment, but fully controlled by a government client and located inside the country. Now starting to be researched by multiple Cloud vendors |
| generative AI | Generative AI is the technology to create new content by utilizing existing text, audio files, or images. With generative AI, computers detect the underlying patterns related to the input and produce similar content. |
| Regulating Big Tech | The growing influence of Big tech companies, resulting in de facto monopolies, poses challenges to the public sector and may lead to unhealthy power dynamics and dependencies as well as to suboptimal services for the citizen (e.g. privacy). Regulation should counterbalance this. |
| Sustainable IT | IT has a twofold impact on the current ecological crisis. First, it reduces the ecological footprint of existing processes. Secondly, It has a considerable ecological footprint throughout its lifecycle (from mining to e-waste). Public sector should maximize the first and minimize the second. |
| Cloud Service Brokerage | Providing support with added value, such as security and integration, to help people to use cloud services efficiently and correctly. |
| Cloud Migration | As the pressure to move solutions to the Public Cloud increases, so does the inherent danger of vendor lock-in. Therefore, Cloud Migration strategies and techniques become a more important defensive measure to safeguard an enterprise’s flexibility in choosing Cloud Service Providers. |
| Open Data | Data interoperability based on documented “open data” for citizens, enterprises, … (and in some cases based on web semantics norms). One of the most important forms of open data is open government data. Mostly there are severe data quality issues. |
| Business Process Management | With more and more services and processes being automated and integrated, management and optimization of it all becomes paramount. BPM is evolving from simple control towards a suite of tools combining traditional automation with management, but also integrating AI. |
| Shadow AI | The phenomenon where individuals (e.g. ‘citizen data scientists’) use easy-to-use tools to develop their own AI-solutions and models. Very powerful for the business, but also dangerous for an untrained audience and in the context of ethical decisions and biased data. |
| Dark/Deep Web | The deep web is the part of the Web not indexed by web search engines. The dark web is the part of the deep web that requires specific software, configurations, or authorization to access. The dark/deep web is generally used for criminal activities. |
| Civic Engagement | The use of IT to stimulate voluntary participation and self-organization of citizens to create societal added value. The citizen can assume one or more roles, such as data provider. |
| Customer support automation | Customer support automation is anything that aims to reduce or eliminate the need for human involvement in solving customer inquiries, for example by automatically answer email questions or even phone calls. It also comprises assistance for call center agents by providing answer suggestions. |
| Legacy Integration | The integration of legacy applications with newer efforts is a constant drag on resources. What can be done to solve this problem more efficiently? |
| Internet of Things / Everything | With the Internet of Things (IoT), many (electromechanical) objects, along with a vast amount of sensors and actuators, become connected to the internet and generate an abundance of data, allowing all kinds of new business. |
| metaverse | A converged network of virtual-reality spaces where users can interact with a computer-generated environment and other users to socialize, buy (virtual) goods, perform work-related activities, etc. |