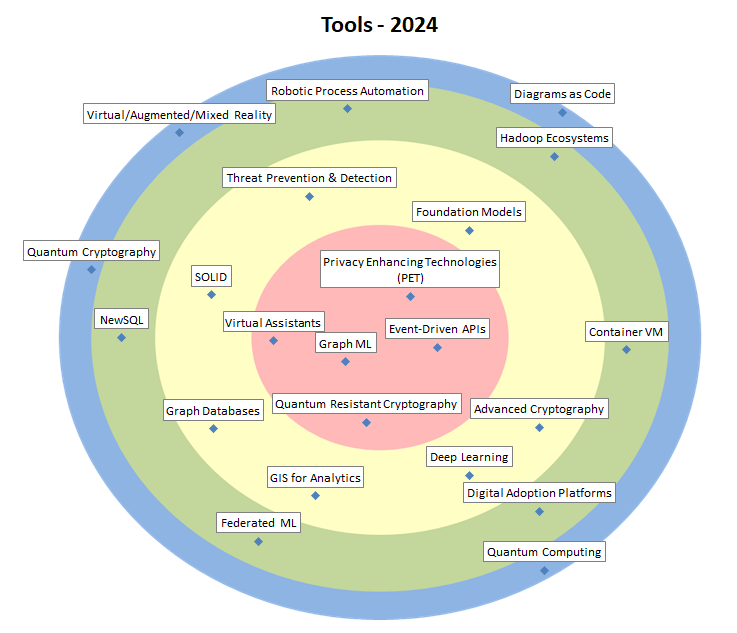
| Privacy Enhancing Technologies (PET) |
= |
Technologies to maximise the usability and usefulness of data consumed by applications, software, and information systems and minimise the amount of personal data used in these applications. PET strive to maximise data security. Examples are pseudonymisation and differential privacy. |
| Event-Driven APIs |
= |
Event Driven Architecture enters the realm of the API’s, with a de facto standard (AsyncAPI) to describe asynchronously communicating API’s. This shows the growing importance of EDA (see also the reactive movement). Now standards and technologies are maturing to formalise this paradigm. |
| Graph ML |
+ |
Graphs are a powerful way of representing entities and their interactions, their representation power are combined with machine learning to make better predictions. |
| Quantum Resistant Cryptography |
+ |
Cryptographic algorithms considered secure against an attack performed by a quantum computer. Most relevant are the NIST standardisation procedure and lattice-based cryptography. |
| Virtual Assistants |
+ |
Virtual Assistants, including Copilots, are software programs designed to assist users in a variety of tasks through natural language processing and AI-driven technologies. Basic tools understand and execute user commands, more advanced tools also provide interaction and follow-up. |
| Foundation Models |
– |
Foundation models are AI models based on transformer architectures. They are generic, trained on broad data and applied to many tasks with little or no extra training. They include large language models (GPT3) and diffusion models (DALL-E). |
| Advanced Cryptography |
= |
Advanced cryptography is cryptography that goes beyond the well-known crypto workhorses such as digital signatures. It allows to reconcile functional requirements with strong security and privacy requirements, which is would otherwise be impossible or at least very complex. |
| Deep Learning |
= |
Important focus area of AI. Architectures such as Recurrent/Convolutional Neural Nets, GANs, etc. learn hierarchical representations of the data, corresponding to different levels of abstractions, largely from the raw data. Toolkits include TensorFlow, Caffe, Keras,… |
| GIS for Analytics |
= |
Analytical software that integrates with GIS (Geographical Information Systems). Allows to represent the results of the analytical software geographically. |
| Graph Databases |
= |
Databases based on and/or oriented towards graphs, with nodes (entities) connected through edges (relations). They are very useful in graph/network analytics, but could also serve in miscellaneous production systems. |
| SOLID |
= |
Solid lets people store their data securely in decentralised data stores called Pods. All data in a pod is accessible via the Solid Protocol. When data is stored in someone’s pod, they control who and what can access it. |
| Threat Prevention & Detection |
+ |
Threat detection is an organisation’s ability to monitor events in its IT environment and detect real security incidents. Threat prevention is the ability to block specific threats before they penetrate the environment or before they do damage. Supporting technologies are e.g. SIEM, PAM & DLP. |
| Hadoop Ecosystems |
– |
Hadoop Ecosystems implement Big Data distributed storage (HDFS), access (Hive, Impala), distributed computing (MapReduce, Spark), transfer (Sqoop, Kafka, Flume), configuration, monitoring, and management modules, in one integrated environment consisting of several nodes. |
| Container VM |
= |
Containers are not perfectly isolated, virtual machines are too heavyweight. Container VM technology aims to bridge the gap by making very lightweight but well isolated VM’s, perfectly suited to run a container. Useful for multitenant Kubernetes and FPaaS platforms. |
| Digital Adoption Platforms |
= |
Digital Adoption Platforms are libraries or toolkits used to create tutorials, step-by-step guides or walkthroughs for the first use of a website or app. Mainly used for onboarding new customers or employees. |
| Federated ML |
= |
Methods to train ML models in a distributed way, where data is kept locally stored and is not exchanged nor centralized. Enabling collaborative learning without compromising data confidentiality, it’s a technical building block for Edge AI. |
| NewSQL |
= |
NewSQL Databases combine the scalability and performance of NOSQL DB’s with the ACID principles of RDBMS. Like the traditional DB’s, they support the relational model and SQL. This makes them more suited to replace these DB’s in older applications being re-engineered to increase resilience. |
| Robotic Process Automation |
= |
Robotic Process Automation is a process automation technology in which software robots can take over keyboard/mouse and other controls to simulate the work of human workers, enabling automation without altering existing systems. |
| Diagrams as Code |
= |
Several interesting tools now exist to define your diagrams along with your code and then to generate them graphically, allowing the diagrams to be kept more consistent with the code, to be versioned, and to be managed more efficiently. |
| Quantum Computing |
= |
Quantum computing is based on quantum-mechanical phenomena. It might in the future allow more powerful simulations and analysis than today. Its fundamentals are strongly deviating from the ones in classical computers. This is reflected in new programming languages such as Q#. |
| Quantum Cryptography |
= |
Quantum cryptography is the science of exploiting quantum mechanical properties to perform cryptographic tasks. The best-known example of quantum cryptography is quantum key distribution which offers an information-theoretically secure solution to the key exchange problem. |
| Virtual/Augmented/Mixed Reality |
= |
UI technologies offering an immersive experience, using altered or completely simulated environments in which the user senses and interacts with virtual entities. Potential uses in public sector could be (explorational) Analytics and field work (inspection). |