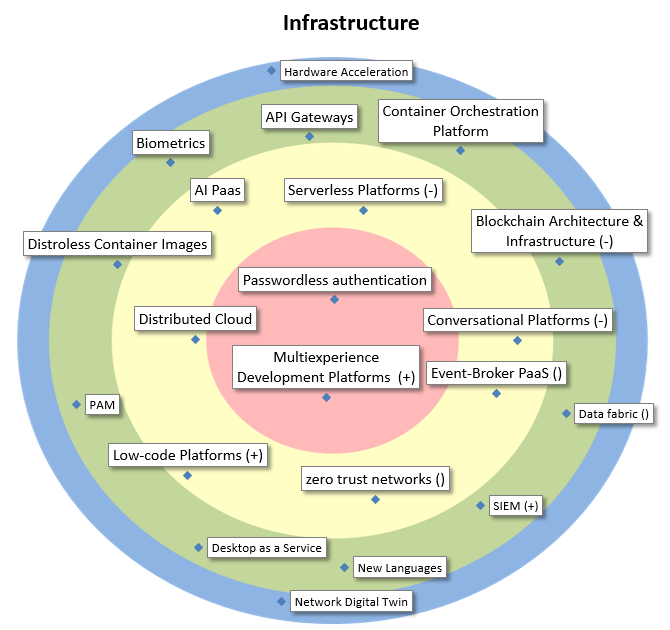
| Passwordless authentication |
Passwordless authentication refers to authentication methods in which a user logs in to a computer or application without entering (and remembering) a password or any other knowledge-based secret. The goal is to provide a higher level of security and convenience. |
| Multiexperience Development Platforms |
Tooling set for developers (front-end development tools and back-end services) to support mobile, modern web, wearable, conversational and AR development, ensuring a consistent user experience across all those interfaces/channels so that users can accomplish their activity seamlessly. |
| Conversational Platforms |
Conversational platforms support the development of conversational interfaces based on intent and entity recognition, context handling, exception handling, messaging platform connectors and monitoring/analytics. |
| Serverless Platforms |
This architecture allows to simply send code, based on handler templates, to a ‘Function Platform as a Service’ (FPaaS). It can then immediately be run without any server or middleware setup. Scalability, robustness, and many other non-fuctional requirements are handled by the platform. |
| AI Paas |
AI Platform as a Service (PaaS) provides AI model building tools, APIs and associated middleware that enable the building/training, deployment and consumption of machine learning models running on prebuilt infrastructure as cloud services. |
| Distributed Cloud |
Implementation of public cloud services in the datacenter of an organization (or another physical location). As such, latency will be better (at the edge) and data remains on site. Operation, governance, updates and evolution of the services are the responsibility of the public cloud provider. |
| Low-code Platforms |
Platforms or frameworks on which developers, and sometimes also business stakeholders, can more rapidly build applications. Delivered through PaaS or as libraries, they are often characterized by the use of graphical programming methods, for GUI but also for the logic. |
| zero trust networks |
The main concept behind zero trust is “never trust, always verify,” which means that devices should not be trusted by default, even if they are connected to a managed corporate network such as the corporate LAN and even if they were previously verified. |
| Event-Broker PaaS |
The heart of an event system, a kind of middleware for EDA. This is, or can be used to build, the Event Bus. These platforms take care of the publish and subscribe mechanics, the delivery guarantees, and sometimes storage and replay. |
| Blockchain Architecture & Infrastructure |
Architectural and infrastructural aspects need to be considered if a blockchain network is set up or when a blockchain-based application is launched. Of particular interest is EBSI, the European Blockchain Services Infrastructure. |
| Container Orchestration Platform |
Containers have become the dominant means of deploying applications on Cloud infrastructure. As such, orchestration and management of containers has become crucial for maintainability and control, allowing an organization to effectively employ thousands of containers in production. |
| API Gateways |
A platform to manage an organization’s APIs. They act as gatekeepers, controlling (and metering, billing) access and making centralized security policy encforcement possible, but also providing documentation and helping developers use the APIs |
| Biometrics |
Biometrics are metrics related to human characteristics (e.g. fingerprint, DNA, facial recognition). Biometrics authentication can be used as access control and finally finds acceptance as a strong authentication on mobile devices. |
| Distroless Container Images |
(quarkus vermelden) Minimal kernel and functionality needed to make a container work for the application it is supposed to support. Decreases weight and increases security. Quarkus is an example for the Java world. |
| PAM |
Privileged Access Management (PAM) refers to a class of solutions that help secure, control, manage and monitor privileged access to critical assets. |
| Desktop as a Service |
A service offering that deploys a virtualized desktop experience, delivered to a customer on demand from a remotely hosted location. |
| New Languages |
Some new upcoming programming languages have interesting properties regarding efficiency/security/robustness/scalability (Rust, Kotlin, WebAssembly, …) that might be useful in particular usecases. |
| SIEM |
In the field of computer security, security information and event management software products and services combine security information management and security event management. They provide real-time analysis of security alerts generated by applications and network hardware. |
| Data fabric |
The data fabric is a distributed data management platform that supports data integration and data sharing. The data fabric can connect to multiple data sources with minimal coding and be accessible to multiple applications. It also eases data sharing between cloud and on-premise data centers. |
| Hardware Acceleration |
Use of specialized hardware to perform time-critical or high-throughput computations (e.g. GPGPU). Useful for big data analytics or highly parallellizable tasks, e.g. in context of machine learning / AI |
| Network Digital Twin |
A digital copy of the company network, for monitoring, analysing the consequences of problematic alterations of the physical network, with roll-back mechanisms. As all (virtual) devices are stored in a database, lookup is very fast and efficient. For critical networks. |